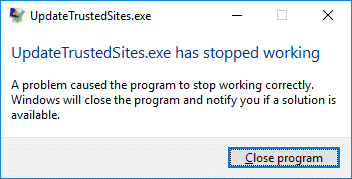
SCCM client agent error UpdateTrustedSites Stopped working – Recently I came across a strange issue related to SCCM client agent installs. One of the customer upgraded their configuration manager setup to version 1606. Post the client push installation, the client agent installed but there were errors post the client installation. Personally I have not come across this error till now. Admins reported SCCM client agent install error UpdatedTrustedSites.exe has stopped working. A problem caused the program to stop working correctly. Windows will close the program and notify you if a solution is available. After clicking Close program button the box appeared again in few minutes.
Most of all checking the event viewer revealed the below info.
Faulting application name: UpdateTrustedSites.exe, version: 0.0.0.0
Faulting module name: unknown, version: 0.0.0.0
Exception code: 0xc0000005
Fault offset: 0x00007ff96c0000c4
Faulting process id: 0x3554
Faulting application path: C:\windows\CCM\UpdateTrustedSites.exe
What is UpdateTrustedSites.exe
When you install SCCM client agent on a computer, one of the component installed is UpdateTrustedSites. This application is located under \Windows\CCM\ folder. Probably this is the file that updates Trusted Sites in Internet Explorer. I am sure there is a setting under client settings > Computer Agent > Add default application catalog website to internet explorer trusted site zones. This setting adds the app catalog website to IE trusted zone. The file behind this setting to work is updatetrustedsites.exe.
SCCM client agent error UpdateTrustedSites Stopped working
Resolution – After performing some troubleshooting, checking few things, this issue was seen on multiple computers. These computers were installed with Windows 10 version 1607. The computers were had Symantec endpoint agent installed. I did a bit of research and I found a link where the exact issue is described. As this file adds websites to trusted zones in IE, the SEP (version 14) treats this activity as malicious. Therefore to ensure SEP doesn’t block this file, add this file to exception policy in the SEPM Console. Doing that should fix this issue. I don’t say this is a solution rather it’s a workaround and should work well. I am sure Symantec is aware of this issue and hopefully this should be fixed soon.